Smishing: 5 Proven Ways To Detect And Avoid Attacks
Unmask the dangers of SMS phishing attacks and arm yourself with proven defenses to safeguard your personal and financial data.
Smishing, a blend of ‘SMS’ and ‘phishing,’ represents a growing cyber threat where attackers exploit text messages to deceive users into surrendering sensitive information or compromising their devices. Unlike traditional email phishing, smishing leverages the trusted nature of mobile SMS, making it highly effective as people check phones constantly and assume texts from unknown numbers hold legitimacy.
Understanding the Mechanics of Smishing Attacks
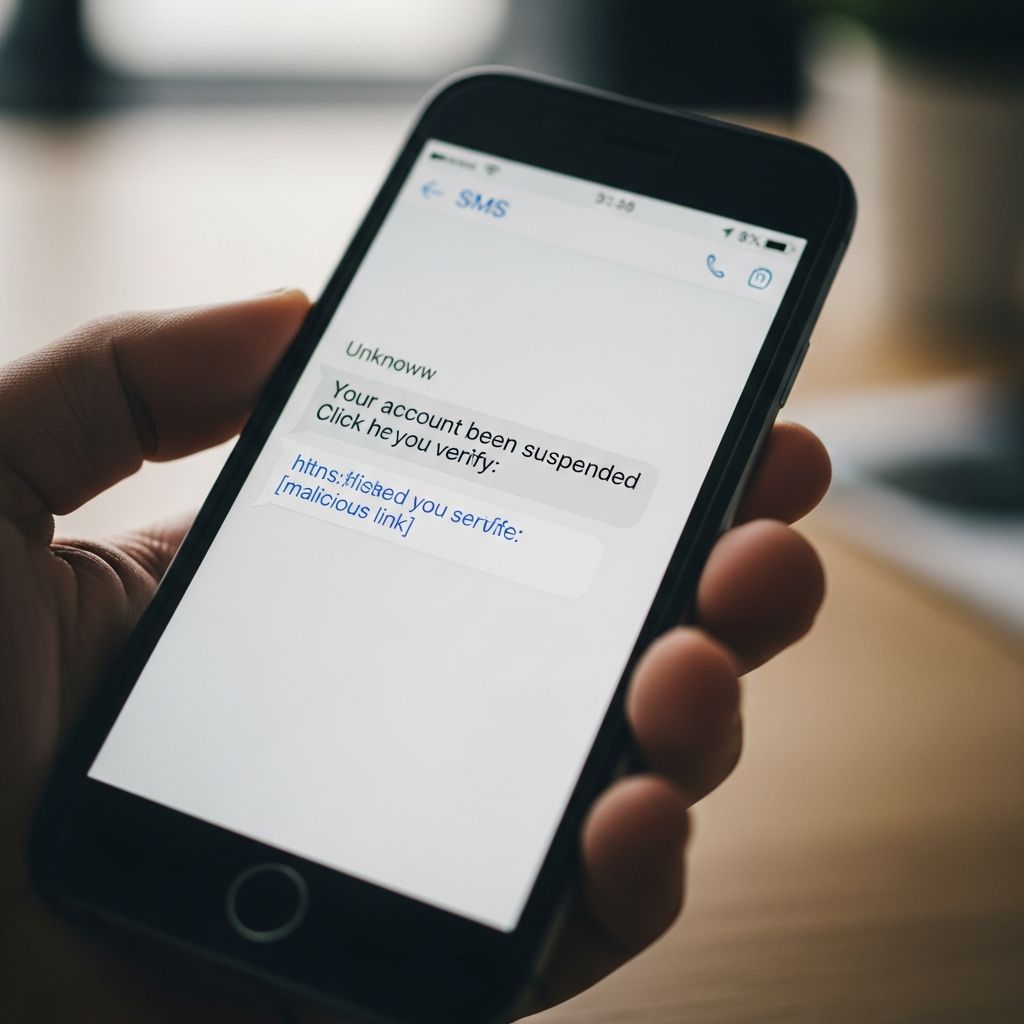
At its core, smishing involves sending fraudulent text messages that mimic legitimate sources, such as banks, government agencies, or popular services. These messages create urgency, prompting recipients to act quickly without scrutiny. Attackers aim to harvest personal data like login credentials, Social Security numbers, or payment details, or to deploy malware via links or downloads.
The rise in smishing stems from smartphones’ ubiquity; users receive texts more readily than emails, with bank impersonation comprising about 10% of all such attacks. Cybercriminals exploit this by crafting messages that appear personalized or official, often including spoofed sender IDs to enhance credibility.
Key Tactics Employed by Smishing Attackers
Smishing relies on social engineering to manipulate emotions like fear, greed, or curiosity. Common techniques include:
- Impersonation of Trusted Entities: Messages pretend to be from banks, retailers, or government bodies, using familiar logos or phrasing to build false trust.
- Urgency and Threats: Texts warn of account suspension, overdue payments, or security breaches, pressuring immediate clicks on malicious links.
- Enticement Offers: Promises of prizes, refunds, or exclusive deals lure victims to fake sites where data is stolen.
- Malware Delivery: Links lead to app downloads that install spyware, granting attackers remote device access.
These tactics evolve rapidly, with attackers using shortened URLs or legitimate-looking domains to bypass basic filters.
Distinguishing Smishing from Other Phishing Variants
While all phishing deceives for gain, smishing is unique to SMS. Here’s a comparison:
| Type | Medium | Common Goal | Example |
|---|---|---|---|
| Smishing | SMS/Text | Click links, share info | Bank fraud alert via text |
| Phishing | Malware/credentials | Fake login page email | |
| Vishing | Phone Call | Real-time info extraction | Impersonated support call |
Smishing’s brevity and direct delivery make it harder to spot than lengthier emails.
Prevalent Smishing Scenarios in the Wild
Attackers draw from real-world patterns to maximize success. Here are documented examples:
- Financial Institution Alerts: ‘Your account is locked. Verify now: [link].’ Leads to phony login portals.
- Government Impersonation: Fake IRS texts claiming tax refunds require SSN submission.
- Delivery or Order Notifications: Unsolicited messages about packages or invoices with malicious tracking links.
- Tech Support Warnings: Claims of device issues urging software ‘updates’ that are malware.
- Reward and Contest Wins: ‘You’ve won a $500 gift card! Claim here.’ Harvests details on fake claim sites.
Advanced variants include ‘pig butchering,’ where scammers build rapport over time via texts before pitching fake investments. Business-targeted smishing mimics executives requesting urgent transfers.
Why Smishing Poses a Greater Risk Today
Mobile dependency amplifies smishing’s danger; 95% of people keep phones nearby, responding faster to texts than emails. Short message limits hinder detailed explanations, and SMS lacks robust spam filters compared to email providers. In 2025, reports indicate smishing incidents surged due to improved spoofing tools, affecting consumers and enterprises alike. Victims face financial loss, identity theft, or corporate breaches from stolen credentials.
Proven Strategies to Detect and Avoid Smishing
Prevention hinges on vigilance and habits:
- Verify Sender Independently: Never use provided links; contact the organization via official app or known number.
- Scrutinize for Red Flags: Unsolicited requests, poor grammar, generic greetings, or pressure tactics signal fraud.
- Avoid Unsolicited Links/Downloads: Hover or preview URLs; legitimate entities rarely demand action via text.
- Enable Device Protections: Use spam blockers, two-factor authentication (non-SMS), and security apps.
- Educate and Report: Train on examples; forward suspicious texts to authorities like 7726 (SPAM) in the US.
For businesses, implement SMS filtering and employee training to curb internal risks.
Real-Life Impact: Victim Stories and Statistics
Smishing drains billions annually. One case involved a traveler receiving a fake hotel bill text post-checkout, nearly leading to a malware download. Another saw ‘wrong number’ texts evolve into investment scams. Stats show 10% of smishing targets banks, with rising CEO fraud via SMS. Recovery is tough; stolen data fuels broader crimes.
Advanced Defenses: Tools and Technologies
Beyond basics, leverage AI-driven threat detection in apps like those from cybersecurity firms, which analyze message patterns in real-time. Carrier-level SMS firewalls block known malicious numbers. For enterprises, endpoint protection scans downloads automatically. Regularly update OS and apps to patch vulnerabilities exploited in attacks.
FAQs: Common Questions on Smishing
What should I do if I receive a suspicious text?
Do not engage. Delete it, block the number, and report to your carrier or FTC.
Can smishing affect businesses?
Yes, via fake executive requests or IT alerts, leading to wire fraud.
Is smishing more dangerous than email phishing?
Often, due to higher trust in texts and quicker responses.
How do attackers get my phone number?
Via data breaches, public lists, or random generation.
Are there apps to block smishing?
Yes, security suites with SMS scanning from reputable providers.
Staying informed empowers you against smishing’s stealthy evolution. Cultivate skepticism for every unsolicited text.
References
- What is Smishing (SMS Phishing)? — SentinelOne. 2024. https://www.sentinelone.com/cybersecurity-101/cybersecurity/what-is-smishing/
- SMS Phishing (Smishing) Examples & Defenses — KnowBe4. 2024. https://blog.knowbe4.com/smishing-examples-defenses
- 6 Types of Smishing Attacks and 5 Ways to Prevent Them — Cynet. 2024. https://www.cynet.com/cybersecurity/5-types-of-smishing-attacks-and-5-ways-to-prevent-them/
- What Is Smishing? Examples, Protection & More — Proofpoint. 2025-02-01. https://www.proofpoint.com/us/threat-reference/smishing
- What Is Smishing? Definition, Examples & Protection Tips — TheSSLStore. 2024. https://www.thesslstore.com/blog/what-is-smishing-definition-examples-protection-tips/
Read full bio of medha deb