Email Spoofing: 5 Common Techniques And 3 Defenses
Understand email spoofing attacks, their mechanisms, real-world impacts, and proven strategies to safeguard your communications and data.
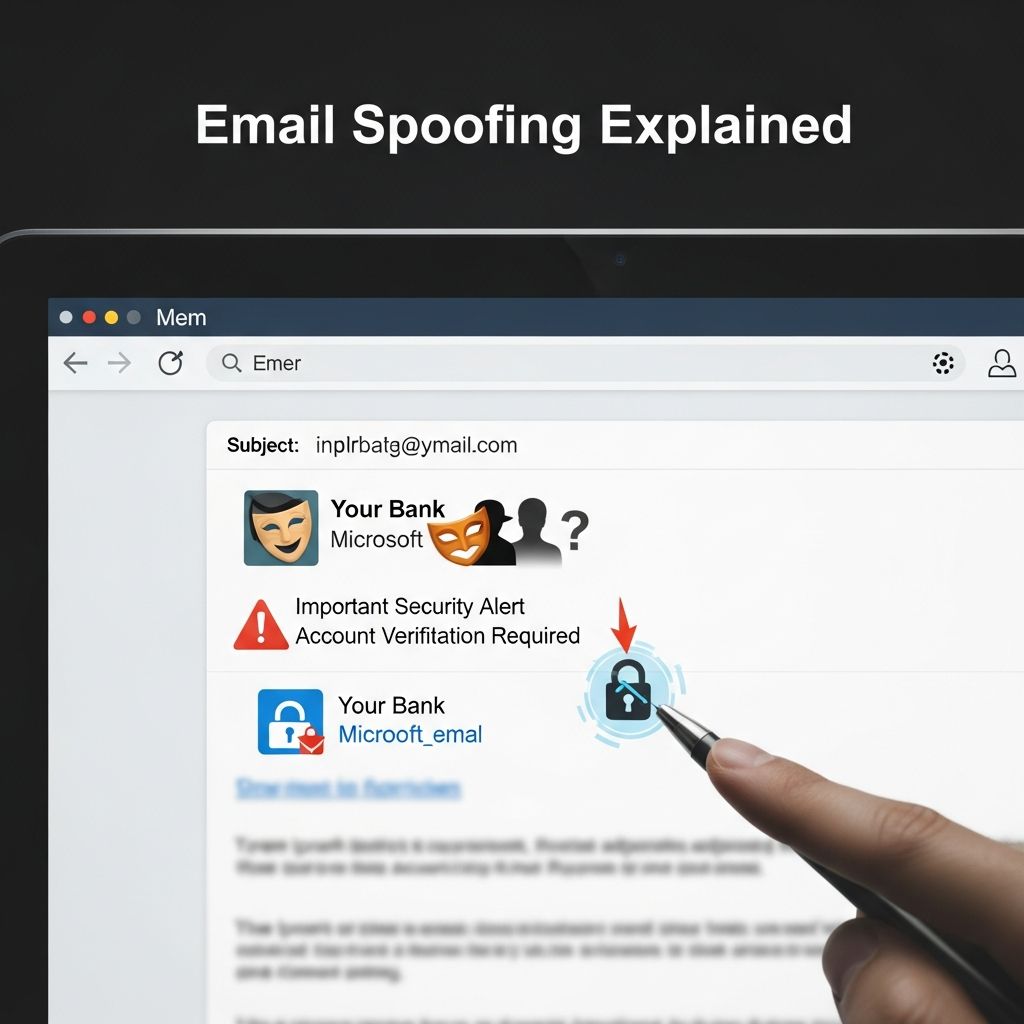
Email spoofing represents a foundational tactic in modern cyber threats, where malicious actors manipulate email headers to disguise their identity and impersonate trusted sources. This deception preys on users’ tendency to trust familiar names or domains, leading to phishing successes, data breaches, and massive financial losses reported at over $2.4 billion in 2021 by the FBI’s Internet Crime Complaint Center.
The Mechanics Behind Forged Emails
At its core, email spoofing involves altering key components of an email’s structure, primarily the headers that dictate how messages are displayed and routed. Standard email protocols like SMTP were designed without robust sender verification, allowing attackers to insert fake “From,” “Reply-To,” and “Return-Path” fields effortlessly. When a recipient opens the message, their email client shows the forged details, often without revealing the true origin unless headers are manually inspected.
This vulnerability stems from the decentralized nature of email transmission, where servers relay messages based on trust rather than strict authentication. Attackers exploit this by crafting messages through open relays or compromised servers, embedding malicious payloads like links to fake login pages or malware-laden attachments.
Key Variants of Spoofing Techniques
Spoofing manifests in several forms, each targeting different aspects of email perception and interaction. Understanding these helps in recognizing and mitigating risks.
- Display Name Spoofing: Here, criminals alter the visible name in the inbox while leaving the underlying email address unchanged or partially masked. Users, relying on the name for quick verification, often overlook the actual domain mismatch.
- Reply-To Manipulation: The “Reply-To” header is changed to redirect responses to the attacker’s controlled address, facilitating follow-up scams without immediate suspicion.
- Header Forgery: Direct tampering with the “From” field creates an illusion of legitimacy from trusted entities like banks or colleagues.
- Lookalike Domain Attacks: Attackers register domains visually similar to legitimate ones, using homoglyphs (e.g., Cyrillic characters resembling Latin ones) or alternate TLDs like .co instead of .com.
- Email Forwarding Exploitation: Compromised accounts have forwarding rules altered to relay spoofed messages seamlessly.
Email Spoofing vs. Related Threats
While often confused with phishing, spoofing is a specific enabler. The table below clarifies distinctions:
| Aspect | Email Spoofing | Phishing |
|---|---|---|
| Definition | Forging headers to fake sender identity | Broad scams tricking users into data disclosure or malware infection |
| Goal | Impersonate trusted sources | Steal credentials, funds, or install malware |
| Techniques | Header manipulation, domain mimics | Fake sites, attachments, social engineering |
| Detection | Requires header inspection | Often via grammar errors or urgent tones |
Real-World Impacts and Notable Incidents
The consequences of email spoofing ripple across individuals and organizations. In Business Email Compromise (BEC), spoofed executive messages trick finance teams into unauthorized transfers. Proofpoint notes cases where attackers impersonate CEOs, leading to multimillion-dollar wire fraud. A classic example: a forged PayPal alert demanding password resets, directing users to credential-harvesting sites mimicking official branding.
High-profile BEC scams have defrauded companies globally, with attackers using reconnaissance to personalize requests. Fake vendor invoices or HR policy updates also proliferate, embedding ransomware via attachments. Globally, these tactics contribute to spam floods and targeted spear-phishing, eroding trust in digital communications.
Spotting Spoofed Messages: Practical Indicators
Detection demands vigilance beyond surface-level checks. Key red flags include:
- Mismatched display names and domains (e.g., “support@paypal.com” from paypat4835761.com).
- Unexpected urgent requests for funds, credentials, or attachments from known contacts.
- Inconsistent greetings, poor grammar, or generic salutations in supposedly personalized emails.
- Hovering over links reveals unrelated URLs; avoid clicking.
- Requests to reply to unusual addresses or bypass standard procedures.
Always inspect full headers via email client options (e.g., “View Source” in Gmail). Legitimate emails align across From, Reply-To, and domain records.
Robust Prevention: Technical and Behavioral Strategies
Defending against spoofing requires layered defenses. Email authentication protocols are paramount:
- SPF (Sender Policy Framework): Domain owners publish TXT records listing authorized sending IPs, blocking mismatches.
- DKIM (DomainKeys Identified Mail): Adds cryptographic signatures to verify message integrity and origin.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): Builds on SPF/DKIM, enforcing policies like quarantine or reject for failures, plus reporting.
Organizations should enforce DMARC with a “reject” policy. User training emphasizes verification: call senders via known numbers, use multi-factor authentication (MFA), and deploy advanced filters like machine learning-based gateways.
Endpoint protection, regular updates, and zero-trust models further harden resilience. For individuals, tools like Proton Mail integrate spoofing checks natively.
FAQs on Email Spoofing
What exactly is email spoofing?
In cybersecurity, email spoofing forges sender addresses to mimic trusted sources, commonly fueling phishing by manipulating headers.
How do attackers perform email spoofing?
They alter From, Reply-To, and other headers using SMTP weaknesses, often via compromised relays or tools, without needing account access.
What’s an example of a spoofing scam?
A fake CEO email requests urgent wire transfers to new vendors, or PayPal alerts link to phishing sites stealing login details.
Can individuals protect against spoofing?
Yes: scrutinize sender details, enable 2FA, use secure providers with DMARC, and report suspicious emails.
Why is BEC particularly dangerous?
It leverages authority trust, bypassing checks for high-stakes actions like fund transfers with minimal technical traces.
Do SPF, DKIM, and DMARC fully stop spoofing?
They significantly reduce it by authenticating domains, but user awareness remains essential against sophisticated variants.
Future Trends and Evolving Defenses
As AI enhances spoofing (e.g., generating convincing prose), defenses evolve with machine learning anomaly detection and stricter protocols like BIMI (Brand Indicators for Message Identification). BIMI displays verified logos in inboxes, adding visual trust cues. Regulatory pushes, like the EU’s NIS2 Directive, mandate advanced email security for critical sectors.
Quantum-resistant cryptography looms for DKIM upgrades, countering future threats. Ultimately, hybrid approaches—tech stacks plus human training—offer the best shield.
References
- What is Email Spoofing? Types & Examples — SentinelOne. 2023. https://www.sentinelone.com/cybersecurity-101/threat-intelligence/email-spoofing/
- What Is Email Spoofing? Definition & Examples — Proofpoint. 2024. https://www.proofpoint.com/us/threat-reference/email-spoofing
- Email Spoofing: Definition & Examples — Hornetsecurity. 2023. https://www.hornetsecurity.com/en/knowledge-base/email-spoofing/
- What is email spoofing? — Proton. 2023. https://proton.me/blog/what-is-email-spoofing
- What Is Email Spoofing? – IT Glossary — SolarWinds. 2024. https://www.solarwinds.com/resources/it-glossary/email-spoofing
- What is email spoofing? — Cloudflare. 2024. https://www.cloudflare.com/learning/email-security/what-is-email-spoofing/
- What is Email Spoofing & How to Identify One — CrowdStrike. 2024. https://www.crowdstrike.com/en-us/cybersecurity-101/social-engineering/email-spoofing/
Read full bio of medha deb

















