Protecting Your Cards: Guide to Fraud Prevention
Essential strategies to safeguard your financial accounts from unauthorized transactions

Protecting Your Cards: A Comprehensive Guide to Fraud Prevention
Understanding the Landscape of Payment Card Threats
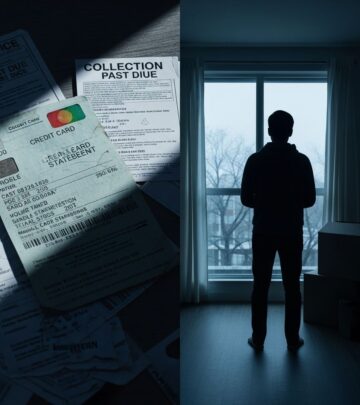
Payment card fraud represents one of the most prevalent financial crimes affecting consumers today. Criminals employ increasingly sophisticated methods to gain unauthorized access to card information and commit fraudulent transactions. Understanding these threats is the first step toward developing an effective defense strategy. The landscape of card fraud continues to evolve, with scammers adapting their tactics to exploit new vulnerabilities in payment systems and consumer behavior.
The financial impact of unauthorized charges extends beyond the immediate loss of funds. Victims often face the stress of dispute resolution, potential damage to their credit ratings, and the time-consuming process of account recovery. By implementing proactive security measures, you can substantially reduce your vulnerability to these threats and respond swiftly if fraud does occur.
Establishing Regular Account Monitoring Practices
One of the most effective defense mechanisms against fraudulent activity is consistent and thorough account monitoring. This practice involves regularly reviewing your financial statements and transaction history to identify any unauthorized charges or suspicious patterns.
The Importance of Frequent Account Reviews
Develop a habit of checking your credit card and bank statements at least weekly. Fraudsters often begin with small, inconspicuous purchases to test whether you notice before attempting larger transactions. By reviewing statements frequently, you catch suspicious activity early, enabling you to report it before significant damage occurs. Even minor unauthorized charges warrant immediate investigation, as they may indicate compromised account information.
Recognizing Patterns and Anomalies
Legitimate financial institutions typically maintain records of your spending patterns. Familiarize yourself with your normal transaction history so you can quickly identify purchases that deviate from your typical behavior. This awareness allows you to distinguish between legitimate charges and potential fraud. Look for transactions in unfamiliar locations, unusual merchant categories, or purchases made when you know you weren’t shopping.
Leveraging Alert Systems and Notifications
Modern banking technology provides real-time notification systems designed to keep you informed of account activity. Taking advantage of these tools creates an additional layer of protection by enabling immediate identification of unauthorized transactions.
Setting Up Transaction Alerts
Most financial institutions offer customizable alert systems that notify you via email or text message whenever a transaction occurs. These notifications serve as an early warning system, allowing you to identify fraudulent activity within minutes rather than days or weeks. Configure alerts for multiple scenarios: every transaction, transactions above a certain threshold, or transactions at specific merchant types. The more comprehensive your alert setup, the faster you can respond to potential fraud.
Advanced Fraud Detection Technologies
Modern banks employ artificial intelligence and machine learning algorithms to analyze transaction patterns and identify suspicious activity that may indicate fraud. These systems flag transactions that deviate significantly from your established spending habits, examining factors such as transaction location, amount, and merchant category. By enabling these proactive monitoring features, you gain the benefit of sophisticated technology working continuously on your behalf, even when you cannot review statements in real-time.
Creating and Managing Strong Access Credentials
Your passwords and personal identification numbers serve as the primary gatekeepers to your financial accounts. Establishing and maintaining robust access credentials significantly reduces the risk of unauthorized account access.
Password Construction Best Practices
Develop passwords that combine uppercase letters, lowercase letters, numbers, and special characters. Avoid using easily guessed information such as birthdays, names, or sequential numbers. Each of your financial accounts should have a unique password, preventing criminals who obtain one password from accessing multiple accounts. Consider using a password manager application to securely store and generate complex passwords, eliminating the burden of memorizing multiple credentials while ensuring they remain virtually unhackable.
Personal Identification Number Security
When entering your PIN at ATMs or payment terminals, protect the keypad from observation by covering it with your hand or body. Criminals sometimes install hidden cameras near payment terminals to capture PIN information for later fraudulent use. Additionally, familiarize yourself with your PIN and avoid writing it down or sharing it with anyone. ATM operators and legitimate financial institutions never request your PIN, so treat any such request as an immediate red flag.
Selecting Secure Payment Methods
Different payment methods offer varying levels of security. By choosing the most secure options available and understanding their protections, you can substantially reduce your fraud risk.
EMV Chip Technology and Contactless Payments
EMV chip-enabled credit cards provide significantly better security than traditional magnetic stripe cards. The chip generates a unique code for each transaction, making it extremely difficult for fraudsters to clone card information through skimming devices. Contactless payment methods, such as tap-to-pay cards and mobile wallets, use encryption and tokenization technologies that generate one-time transaction codes, further protecting your card details. Whenever merchants offer these options, choose them over traditional swiping methods.
Mobile Wallet and Digital Payment Solutions
Digital payment platforms such as Apple Pay and Google Pay employ tokenization, which replaces your actual card number with an encrypted token valid only for that specific transaction. These methods provide an additional security layer by preventing merchants from seeing your complete card information. Mobile wallets also often require biometric authentication, adding another security barrier against fraudulent use.
Protecting Personal Information from Exposure
Criminals obtain card information through various methods, from data breaches to targeted phishing schemes. Minimizing the exposure of your sensitive information reduces the pathways through which your data can be compromised.
Recognizing and Avoiding Phishing Attempts
Phishing involves criminals impersonating legitimate financial institutions through email, text, or phone calls to trick you into revealing sensitive information. Legitimate companies never request personal information through unsolicited communications. Before responding to any request for financial details, independently verify the request by contacting your bank using the phone number on your statement or their official website. Be suspicious of urgent language, threats of account closure, or requests to “confirm” information you already provided.
Securing Physical Card Information
Handle your physical credit cards with the same care as cash. Never leave cards unattended in public spaces, and store them in secure locations at home. When making purchases, keep your card visible during transactions to ensure merchants don’t process it out of view. Protect the card’s back side when providing it to merchants to prevent others from seeing your CVV security code. When you no longer need a card, destroy it completely rather than simply discarding it in the trash.
Detecting Skimming Threats at Payment Terminals
Card skimming involves criminals installing devices on legitimate payment terminals to capture card information without your knowledge. Developing awareness of these threats allows you to avoid compromised devices.
Identifying Suspicious Card Readers
Before inserting your card into any payment terminal, examine it for signs of tampering. Check whether the card reader appears to be securely attached, whether any parts seem loose or protrude awkwardly, and whether the keypad feels unusual or has a sticky texture. ATMs installed directly inside bank branches generally receive more security oversight than remote machines. Gas pump readers represent particularly common skimming targets, so inspect them carefully and consider using payment methods that don’t require card insertion.
Environmental Awareness and ATM Safety
Use ATMs located in well-lit, populated areas where suspicious activity is more likely to be noticed. Avoid ATMs in isolated locations or those with limited visibility. Be aware of your surroundings when accessing an ATM, and consider using ATMs within bank branches during business hours when security presence is greatest. If something about a terminal seems off or unfamiliar, trust your instincts and use a different machine.
Responding Immediately to Suspected Fraud
Despite preventive efforts, fraud can still occur. Your response speed significantly impacts the extent of potential financial damage and recovery difficulty.
Contacting Your Financial Institution
Upon discovering unauthorized transactions, immediately contact your bank or credit card issuer’s fraud department. Most institutions maintain dedicated fraud divisions available around the clock. When you report fraud promptly, your bank can freeze your account, block additional unauthorized transactions, and begin the dispute resolution process. The faster you report, the more effectively your institution can prevent further misuse of your compromised information.
Updating Compromised Credentials
After discovering fraud, immediately change passwords for all financial accounts and any other accounts using similar credentials. Create entirely new, strong passwords combining uppercase and lowercase letters, numbers, and special characters. This action prevents criminals from using stolen passwords to access other accounts. If you used the same password across multiple accounts, consider this a critical vulnerability requiring immediate attention.
Filing Formal Fraud Alerts
Contact one of the three major credit reporting bureaus—TransUnion, Equifax, or Experian—to place a fraud alert on your credit report. You only need to contact one bureau, as they share alert information with the others. A fraud alert signals to creditors that they should verify your identity more thoroughly before approving new credit accounts in your name, preventing criminals from opening fraudulent accounts on your behalf.
Federal Trade Commission Reporting
If the fraudulent activity involves identity theft or extensive unauthorized transactions, file a complaint with the Federal Trade Commission at IdentityTheft.gov. This creates an official record of the fraud and provides guidance on recovery steps. FTC complaints also contribute to law enforcement efforts to combat fraud rings and criminal networks.
Implementing Long-Term Protective Measures
Beyond immediate fraud response, several long-term strategies provide ongoing protection against future fraudulent activity.
Credit Report Monitoring and Review
Obtain free copies of your credit report annually from all three bureaus and review them carefully for accounts you don’t recognize or inquiries you didn’t authorize. Unauthorized accounts appearing on your credit report indicate identity theft, requiring immediate action. By monitoring your credit reports regularly, you detect identity theft much earlier than you might discover fraudulent charges on your billing statements.
Credit Freezes and Security Freezes
Consider placing a security freeze on your credit report, which prevents creditors from accessing your credit information without your permission. This effectively blocks criminals from opening new accounts in your name, though it also prevents you from opening new credit until you remove the freeze. Security freezes provide powerful protection against identity theft and account fraud.
Identity Theft Protection Services
Third-party identity theft protection services monitor your credit report, alert you to suspicious changes, and provide tools for fraud recovery. Some services include insurance to cover losses resulting from identity theft. While not mandatory, these services add a professional monitoring layer for individuals particularly concerned about theft risk or who have previously experienced fraud.
Understanding Your Rights and Protections
Federal law provides significant protections for credit card fraud victims. Understanding these protections helps you navigate the dispute process with confidence.
Credit card holders typically have limited liability for unauthorized transactions—in many cases, zero liability if you report fraud promptly. Payment processors and card networks operate fraud protection systems designed to investigate disputes and resolve them in your favor when evidence supports your claim. These protections don’t eliminate the inconvenience of fraud, but they do protect your finances.
Creating a Personal Security Action Plan
Consolidate your fraud prevention knowledge into a personalized action plan addressing your specific risk factors and financial situation. This might include:
- Scheduling weekly account review reminders
- Documenting your normal spending patterns for comparison
- Setting up transaction alerts for all accounts
- Creating unique, complex passwords for each financial account
- Storing passwords securely using a password manager
- Planning quarterly credit report reviews
- Establishing protocols for handling suspicious activity
- Maintaining contact information for your bank’s fraud department
Conclusion
Credit card fraud prevention requires a multi-faceted approach combining awareness, technology, and vigilant monitoring. By implementing the strategies outlined in this guide—from regular account reviews and strong passwords to secure payment methods and rapid response protocols—you significantly reduce your vulnerability to fraudulent activity. While no approach guarantees complete immunity from fraud, these comprehensive measures substantially lower your risk and enable swift recovery should fraud occur. Your financial security depends on consistent application of these protective practices combined with awareness of emerging fraud tactics.
References
- Card Payment Fraud: Common Schemes & How to Prevent Them — Unit21. https://www.unit21.ai/fraud-aml-dictionary/card-payment-fraud
- How to Prevent & Protect Against Latest Credit Card Frauds — Bank of America Business. https://business.bofa.com/en-us/content/latest-credit-card-frauds-prevention.html
- How to Avoid Credit Card Scams — University of Minnesota Credit Union. https://www.umcu.org/learn/resources/blogs/how-to-avoid-credit-card-scams
- Six Types of Payment Fraud—and How Businesses Can Prevent Them — Stripe. https://stripe.com/resources/more/six-types-of-payment-fraud
- How to Help Prevent Credit Card Fraud — Equifax. https://www.equifax.com/personal/education/credit-cards/articles/-/learn/how-to-help-prevent-credit-card-fraud/
- What Are Common Types of Credit Card Fraud? — Synovus. https://www.synovus.com/personal/resource-center/fraud-prevention-and-security-hub/fraud-hub-education-and-prevention/featured/types-of-credit-card-fraud/
- Visa Credit Card Security & Fraud Protection — Visa. https://usa.visa.com/support/consumer/security.html
Read full bio of Sneha Tete