Card Skimming Guide: How To Protect Your Money In 2025
Discover the hidden dangers of card skimming, advanced detection techniques, and proven strategies to safeguard your financial data from thieves.
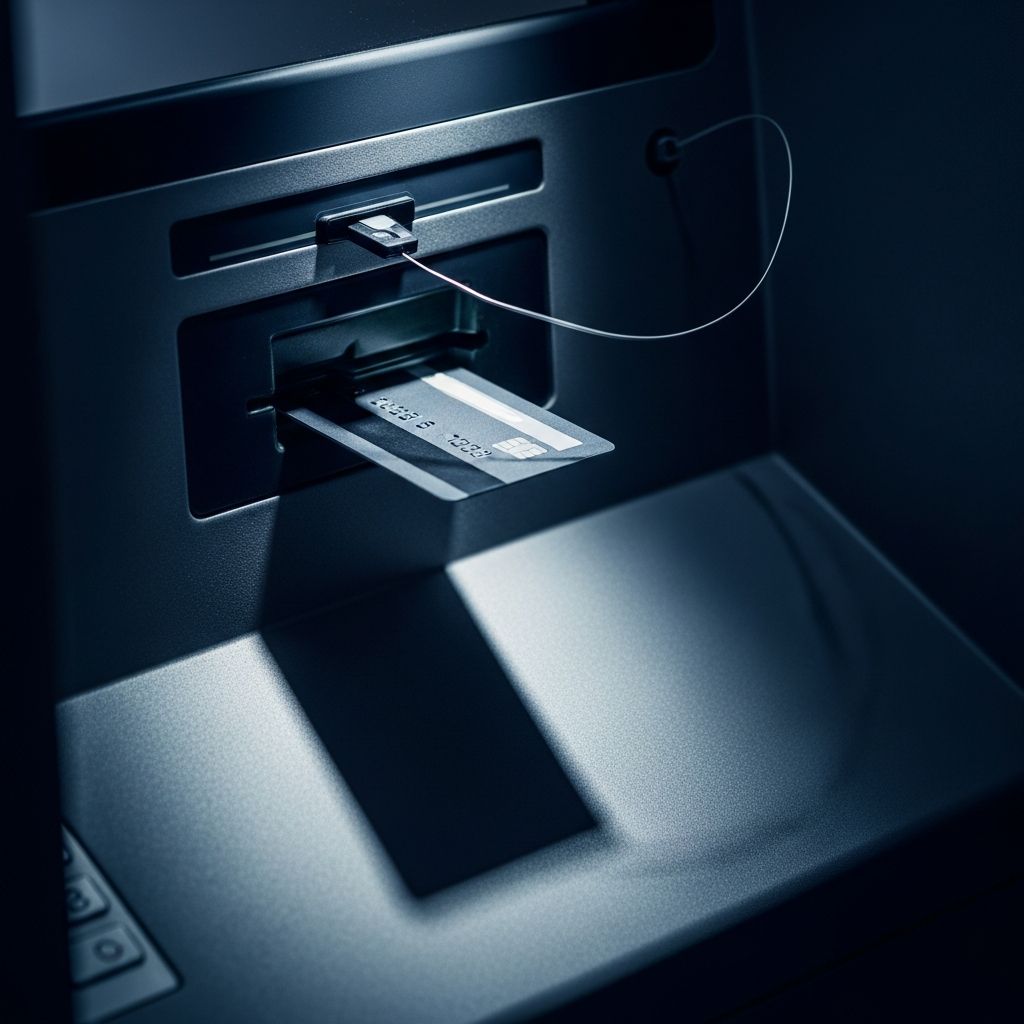
Card skimming represents a pervasive threat in today’s payment landscape, where criminals deploy compact devices to harvest sensitive data from debit and credit cards during everyday transactions. These tools capture essential details like card numbers, expiration dates, and PINs, enabling fraudsters to produce counterfeit cards or execute unauthorized online purchases. Operating covertly at ATMs, gas pumps, and retail point-of-sale (POS) terminals, skimmers blend seamlessly with legitimate hardware, often evading detection for weeks.
This form of theft has surged with the rise of portable electronics, allowing perpetrators to install devices in mere seconds and retrieve stolen data remotely via Bluetooth or cellular connections. Unlike overt robberies, skimming inflicts damage silently, potentially draining accounts before victims notice. Understanding its mechanics empowers individuals and businesses to implement defenses that disrupt these schemes at every stage.
The Evolution of Skimming Technology
Skimming originated with basic magnetic stripe readers but has advanced dramatically. Early devices required physical retrieval, limiting their scope. Modern iterations feature wireless transmission, micro-cameras for PIN capture, and even shimmers—ultrathin inserts targeting EMV chip cards.
- Magnetic Stripe Skimmers: Overlay the original reader, duplicating data from swiped cards. Vulnerable to older cards without chips.
- Chip Shimmers: Slender enough to fit inside slots, extracting partial chip data for cloning despite EMV protections.
- Keypad Overlays and Pinhole Cameras: Record keystrokes and monitor hands, pairing with reader data for full account compromise.
- Digital Skimming (e-skimming): Malicious code on websites intercepts details during online checkouts, bypassing physical hardware.
These innovations exploit transition periods in payment tech, such as lingering magstripe support. Criminals often test installations in low-risk areas before scaling to high-traffic spots.
Prime Targets: Where Skimmers Thrive
Crooks favor locations offering quick access and minimal oversight. Outdoor ATMs and isolated gas pumps top the list due to infrequent inspections and natural camouflage opportunities.
| Location | Risk Factors | Prevalence |
|---|---|---|
| Outdoor ATMs | Remote placement, poor lighting | High |
| Gas Station Pumps | Exposed slots, low foot traffic | High |
| Convenience Stores | Countertop POS, brief unattended moments | Medium |
| Indoor Bank ATMs | Surveillance, staff presence | Low |
Businesses face insider threats too, where employees or contractors attach portable readers to backend systems. Globally, incidents correlate with tourism hubs and cash-heavy economies, underscoring the need for vigilance everywhere.
Decoding Skimmer Hardware: What to Spot
Identifying tampering demands a systematic 10-15 second inspection before every use. Legitimate readers feel integrated and secure; fakes often betray themselves through subtle flaws.
- Visual Mismatches: Compare adjacent readers—differing colors, fonts, or protrusions signal overlays.
- Tactile Tests: Tug gently on edges; loose components or bulkiness indicate add-ons. Authentic parts resist manipulation.
- Surface Irregularities: Scratches around slots, adhesive residue, or uneven seams from hasty installation.
- Hidden Tech: Tiny holes for camera lenses near keypads or unusual protrusions housing batteries.
For shimmers, probe the chip slot with a fingernail; resistance or thin barriers suggest intrusion. Businesses should deploy EMV-compliant terminals and conduct daily sweeps.
Payment Choices That Outsmart Skimmers
Opting for secure methods renders stolen data worthless. Contactless payments generate dynamic codes per transaction, defying cloning attempts.
- Contactless Tap: NFC tech creates one-time tokens, sidestepping stripe and chip vulnerabilities.
- EMV Chip Inserts: Produce unique cryptograms, unlike static magstripe info.
- Digital Wallets: Apple Pay, Google Pay tokenize cards, shielding real numbers even on compromised sites.
- Virtual Cards: Issuer-generated temporaries limit exposure for online use.
Debit cards pose higher risks due to direct account access; favor credit for its $0 liability policies under U.S. regulations.
Behavioral Defenses: Everyday Habits for Protection
Proactive routines minimize exposure without altering routines drastically.
- Select Supervised Machines: Prioritize indoor, camera-monitored ATMs and well-lit pumps.
- Shield Inputs: Cup hand over keypads universally to foil cameras.
- Avoid Risky Spots: Skip standalone kiosks; transact inside stores when feasible.
- Enable Vigilance: Pause for checks, even in familiar venues.
Train household members and staff similarly, fostering a culture of caution.
Digital Vigilance: Fortifying Online Transactions
e-Skimming plagues e-commerce via injected scripts on checkout pages. HTTPS verifies transmission security but not site integrity.
- Confirm padlock icons and avoid suspicious URLs.
- Employ wallet apps for tokenization.
- Activate virtual numbers from providers like Capital One.
Businesses must scan sites continuously and enforce PCI DSS standards to block code insertions.
Monitoring Mastery: Catching Fraud Early
Real-time oversight transforms potential disasters into minor inconveniences. App notifications flag anomalies instantly.
- Daily Reviews: Scan pending transactions via mobile banking.
- Threshold Alerts: Notify for spends over $10 or unusual merchants.
- Multi-Factor Confirmation: Verify texts before responding, dodging phishing.
Spotting fraud within hours caps losses under federal timelines, often with full reimbursement.
Business Armor: Enterprise-Level Countermeasures
Merchants bear PCI compliance burdens, including terminal hardening and staff training.
- Tokenize stored data, eliminating raw card retention.
- Schedule audits and endpoint detection.
- Develop breach response protocols for swift containment.
Integrated fraud tools from banks like Truist provide limits and analytics.
Responding to Compromise: Swift Action Steps
If fraud surfaces:
- Contact issuer immediately to freeze cards.
- File police and FTC reports (IdentityTheft.gov).
- Request new cards and update recurring payments.
- Review statements for 12 months post-incident.
Credit monitoring services track misuse across accounts.
Frequently Asked Questions
What exactly occurs during a skimming attack?
A device intercepts card data and PINs covertly, transmitting them for fraudulent replication.
Are chip cards fully immune to skimming?
No, shimmers target chips, but they generate unusable dynamic data unlike stripes.
How soon should I act on suspicious transactions?
Within minutes via app alerts to minimize liability.
Can I detect skimmers on contactless readers?
Less common, but inspect for overlays; prefer NFC to avoid slots.
What if my business suspects skimming?
Isolate terminals, notify acquirers, and audit PCI compliance.
Future-Proofing Against Emerging Threats
Biometrics and end-to-end encryption promise reduced reliance on cards. Stay informed via issuer updates, as tech evolves rapidly.
References
- Understanding Skimming and How to Prevent It — Flagright. 2024. https://www.flagright.com/post/understanding-skimming-and-how-to-prevent-it
- How To Defend Against Card Skimming and Shimming — Truist Bank. 2024. https://www.truist.com/resources/commercial-corporate-institutional/fraud/articles/how-to-defend-against-card-skimming-shimming
- How to Help Prevent Card Skimming — City National Bank. 2024. https://www.cnb.com/personal-banking/insights/card-skimming-prevention.html
- Understanding Card Skimming and How to Prevent It — SELCO Community Credit Union. 2024. https://www.selco.org/education-articles/understanding-card-skimming-and-how-to-prevent-it/
- Skimming Prevention: Overview of Best Practices for Merchants — PCI Security Standards Council. 2010. https://www.pcisecuritystandards.org/documents/skimming_prevention_overview_one_sheet.pdf
- What Is Card Skimming and How Can You Avoid It? — Experian. 2024. https://www.experian.com/blogs/ask-experian/what-is-card-skimming/
Read full bio of Sneha Tete

















